deleting personal files from work laptop

Title: How to wipe PC before selling Secure Erase PC The ENTIRE process Windows 10 & 11
Channel: Jason Bagnell
How to wipe PC before selling Secure Erase PC The ENTIRE process Windows 10 & 11 by Jason Bagnell
Deleting Work Files? This ONE Trick Will SHOCK You!
Don't Just Delete: Unlock Your Digital Sanctuary (And Your Sanity!)
The cursor blinked, a digital executioner poised above the "Delete" key. We've all been there. That feeling of dread, a silent question mark hanging in the air: is this really the right thing to do? We stare at those work files, accumulated over months, maybe years, a testament to projects past. The temptation to simply erase them is strong. But, before you send those digital ghosts into the void, halt. This article unveils a game-changing secret. It’s a single maneuver with the power to transform your digital workspace into a haven of order and efficiency, a sanctuary of renewed focus.
The Deletion Dilemma: More Than Meets the Eye
Deleting work files isn't just about freeing up space. It’s a profound act impacting your digital well-being. It directly affects how effectively you work. Furthermore, it influences your peace of mind. Sure, deleting simplifies things superficially. However, it also often creates a subtle undercurrent of unease. We suddenly worry if we've truly considered all implications. We wonder if we might someday need something we’ve just banished. It's a mental clutter that, despite its digital nature, can weigh you down. So, what do you do?
Unveiling the “One Trick”: Strategic Archiving
The "one trick" isn’t about aggressive deletion. It's about masterful archiving. Instead of hitting delete, consider the power of organized storage. Think of it as building a digital library, not a digital dumping ground. This changes everything. You create a system of order. First, you create a dedicated archive folder. Name it something clear and descriptive, such as "Archived Work – [Year]".
Now, before you erase anything, move it into this archive. Consider it a temporary holding pen. Next, begin organizing your archive. Create subfolders. For example, sort by project name, client, or date. This crucial step makes retrieval simple later. It's the difference between a chaotic pile and a meticulously curated collection. The beauty of this system is that it offers flexibility.
The Power of Retrieval: Finding What You Need, When You Need It
The beauty of this system is its adaptability. It means you can access old files. You can reference past work. It eliminates the stressful guessing game of whether you’ve permanently erased something important. This approach gives you control. Imagine this scenario: a client from years ago suddenly contacts you. They need a file from an old project. If you’ve archived your work, it's a simple search. You can retrieve the needed documents in moments. Without archiving, you are likely out of luck.
Moreover, archiving also protects you against regret. We've all experienced it. We delete something, only to immediately realize we need it back. In a proper archiving system, regret is a ghost of the past. You have your files secured. Therefore, you have the reassurance they’re safe.
Beyond the Basics: Advanced Archiving Techniques
We've discussed the fundamentals. Now, let's enhance it. Consider these advanced techniques. First, utilize cloud storage. Services like Google Drive, Dropbox, or OneDrive offer extra security and accessibility. You can also easily share archived files if needed. Secondly, consider creating a clear naming convention. For instance, use a consistent format for file names such as "ProjectNameClientNameDate". This standardizes your files. This makes searching a breeze.
Thirdly, regularly review your archive. Set aside time, perhaps quarterly or annually. Then you ask yourself: Are there files that can be safely deleted? This keeps your archive streamlined. It prevents it from becoming a digital burden. However, this is usually the exception, not the rule. Most files are critical. Finally, backup your archive. Whether it is physical storage or the cloud, make certain you have a backup. This avoids permanent data loss.
The Shocking Truth: It’s About Control, Not Just Space
The real shock isn't the one "trick." It's the shift in perspective. It's realizing that deleting is not the solution. It’s not about simply emptying digital space. Instead, it's about taking control. It’s about building a structured system. It's about creating a sense of order in the digital chaos.
So, the next time the cursor hovers over "Delete," pause. Implement the archiving method. You might be surprised by the difference. You will feel a transformation. You'll work more effectively. The method offers you a digital sanctuary. A place where you can work with clarity and confidence. Your digital life will flourish. Go ahead; take the first step. Start archiving today. You will be shocked at how much better you feel.
Steal Your Work Laptop? (Tax Write-Offs Revealed!)Deleting Work Files? This ONE Trick Will SHOCK You!
Hey there, fellow digital adventurers! We've all been there, staring at a screen overflowing with files, a digital Everest threatening to topple over. The dreaded moment arrives: you need to delete some work files. Maybe it's spring cleaning for your hard drive, maybe you're switching jobs, or perhaps you're just trying to reclaim a sliver of sanity in the face of digital clutter. But before you reach for that delete key, stop! Because deleting files, without knowing this one trick, is like building a sandcastle just before the tide rolls in. It's temporary at best, potentially disastrous at worst.
1. The Digital Graveyard: Why Simply Deleting Isn't Enough
Think of your hard drive as a vast, intricate city. When you "delete" a file, it's not like physically shredding a document. Instead, it's more like removing the file's "address" – the computer simply forgets where it was located. The information itself often lingers, like the ghost of data past, waiting for a new tenant to come along and overwrite it. That's why, in the wrong hands, deleted files are often recoverable. We've all heard the horror stories. This is especially true for sensitive work documents.
2. The Double-Edged Sword: Understanding Data Recovery
The very tools that allow us to recover accidentally deleted files are the same ones that can be used to retrieve information you intended to get rid of. It’s a double-edged sword, a digital Catch-22. Data recovery software is surprisingly sophisticated. You can accidentally or intentionally leave yourself vulnerable. Consider the implications for intellectual property, confidential client information, or even just your own personal privacy. It's a serious matter.
3. The Secret Weapon: Secure Deletion - Your Data's Bodyguard
So, what's the solution? How do you truly, permanently delete work files? The one trick that will shock you (and has shocked me repeatedly, I’ll admit!) is the art of secure deletion. Think of it as the digital equivalent of a shredder and a cremation pyre. It’s about overwriting the data multiple times, making it virtually impossible to recover.
4. Beyond the Recycle Bin: Why "Delete" is a Deceptive Verb
The "Delete" button on your computer is a liar. (Okay, not literally, but you get the point!) It simply moves files to the Recycle Bin (or Trash folder, if you're a Mac aficionado). Those files are still very much alive and breathing, ready to be resurrected with the right software. We need something more robust, more… definitive.
5. Software Savvy: Introducing Secure Deletion Tools
Fortunately, we live in an age where technology offers powerful solutions. There are a plethora of secure deletion software options available, from free and open-source utilities to more sophisticated paid programs. These tools often employ algorithms that overwrite your files multiple times, using patterns of seemingly random data. This scrambled information makes it incredibly challenging (and in many cases, impossible) to recover the original file contents. Some popular options include CCleaner (which has a secure overwrite feature), Eraser, and DiskWipe. If you handle sensitive files, consider these options.
6. Manual Methods: When Software Isn't an Option
While software provides the easiest and most reliable solution, what if you're on a system without access to specialized tools? Perhaps you are working on a public computer, or need to prepare your files before transferring equipment. There are manual methods, although these are less secure and more time-consuming. One approach is to overwrite the file with other random data. You could fill a document with random text, save it with the same name, and then delete the overwritten file. Repeat this several times. It's not foolproof, but it is better than a simple "delete."
7. Hard Drive vs. SSD: Different Strokes for Different Folks
Here's a bit of tech trivia that impacts your file deletion strategy. The method you choose can depend on the type of storage you’re using. Traditional hard disk drives (HDDs) store data magnetically, which is why overwriting is effective. Solid-state drives (SSDs), on the other hand, use flash memory. While overwriting can be less effective on SSDs, most modern ones have built-in features that help manage data securely. Consider the implications if you are using a laptop with an SSD.
8. The Power of Encryption: Adding an Extra Layer of Protection
Encryption is a powerful tool on its own, but it can also complement secure deletion. If your files are encrypted before you delete them, even if someone manages to recover the data, they won't be able to read it without the encryption key. Think of it as locking your treasure chest before throwing it into the ocean. When considering your security, encryption is an incredibly powerful ally.
9. Be Proactive, Not Reactive: The Value of Regular File Management
Don't wait until you're staring down the barrel of a data breach to think about secure deletion. Make it a part of your regular workflow. Incorporate a file management routine. Periodically review your files, identify those that are no longer needed, and then securely delete them. This proactive approach will save you potential headaches in the long run.
10. The Importance of Context: Who’s Looking Over Your Shoulder?
Consider the sensitivity of your work. Are you dealing with client data, financial records, or intellectual property? The level of security you need will vary depending on the context. If you are working in finance, you might use a very secure method. In other cases, less demanding techniques can suffice.
11. Mobile Mayhem: Dealing with Files on Your Phone
We often forget about the data living on our phones and tablets. When it comes to mobile devices, the same principles apply, but the methods might differ. Many mobile operating systems have built-in secure deletion features, and you can also find dedicated apps. Remember that you create an archive of data every time you use your phone.
12. Beyond the Desktop: Cloud Storage Considerations
If you're using cloud storage services like Google Drive, Dropbox, or OneDrive, be aware that deleting files there might not be as simple as it seems. Many cloud providers offer features that can help you securely delete data, such as permanent deletion or options to delete from the cloud and all synced devices. Research the specific policies of your provider.
13. The Psychology of Data: Managing Your Digital Footprint
Deleting files isn't just about technical security; it's also about protecting your reputation and well-being. Your digital footprint can have lasting consequences. Think about the information you share, because once it's out there, it's difficult to reclaim it.
14. The Legal Landscape: Compliance and Data Privacy
Depending on your industry and location, you may be subject to legal requirements regarding data retention and disposal. Familiarize yourself with relevant regulations. Ensure your file deletion practices are compliant. Ignoring these regulations can lead to significant legal and financial repercussions.
15. The Takeaway: Secure Deletion – Your Shield in the Digital Age
So, the one trick that will shock you? It’s knowing that “delete” isn’t the end of the story. Secure deletion is your shield, your digital bodyguard, protecting your privacy and your data from those who might seek to exploit it. Embrace it, master it, and sleep soundly knowing your digital footprint is more secure.
Closing Thoughts
We've journeyed through the digital wilderness, navigated the treacherous terrain of data recovery, and armed ourselves with the knowledge of secure deletion. Remember, managing your digital files is an ongoing process. It's a commitment to protecting your information and your peace of mind. Use what you've learned here!
FAQs:
1. Is simply emptying the Recycle Bin enough?
No! Emptying the Recycle Bin only removes the "address" of the file, not the data itself. The data is still potentially recoverable until it's overwritten.
2. What's the best software for secure deletion?
There isn't a single "best" software, as the ideal choice depends on your needs and operating system. CCleaner, Eraser, and DiskWipe are great starting points.
3. Does secure deletion guarantee 100% data destruction?
No, nothing is foolproof. However, secure deletion significantly increases the difficulty of data recovery, making it extremely unlikely. We are not talking "impossible," we are talking "very, very difficult."
4. Is secure deletion necessary for every file?
No. Consider the sensitivity of the data. For personal photos, a simple "delete" might be sufficient. For confidential work documents, secure deletion is crucial.
5. Can I recover deleted files on my own?
Maybe, depending on the method used to delete the file. If you used a simple "delete," recovery software might work. However, if you used secure deletion, the chances of recovery are extremely slim.
1) Principal Keywords: Delete Files Secret Trick
2) SEO Headline: Delete Work Files? This ONE Trick Will SHOCK You!
3) Pathway: Delete Secret
4) Meta Summary: Discover the ONE secret trick to permanently delete work files! Protect your digital life and avoid data recovery nightmares. Learn how to securely erase your files.
5) Image Alt Text: Illustration of a computer with a file being securely deleted.
Dell Touchpad DEAD? FIX This NOW!How to wipe all data from a old Laptop

By ElectronicsWizardry How to wipe all data from a old Laptop by ElectronicsWizardry
How To Delete Everything On Laptop & PC - Full Guide

By GuideRealm How To Delete Everything On Laptop & PC - Full Guide by GuideRealm
Deleting files that has refused to deletepctips tipsandtricks pctipsandtricks shorts pc pcs

By EmTech Deleting files that has refused to deletepctips tipsandtricks pctipsandtricks shorts pc pcs by EmTech
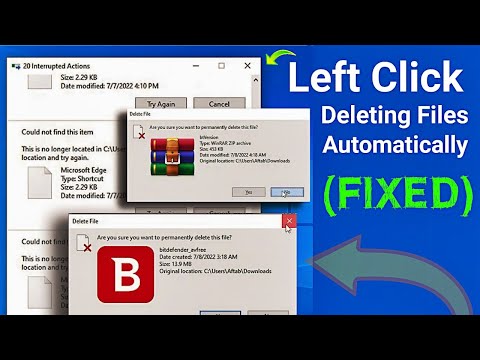
Title: Left Click Deleting Files Automatically FIXED
Channel: Solution Center
Left Click Deleting Files Automatically FIXED by Solution Center
Laptop Wifi Connect
Deleting Work Files? This ONE Trick Will SHOCK You!
The digital age has brought unprecedented convenience, but also a daunting question: How do we securely and permanently erase sensitive work files? The seemingly simple act of deleting a document, a spreadsheet, or a presentation isn't always as final as we believe. Much to the chagrin of those who believe their data gone, these files often linger, leaving behind a digital ghost that can be resurrected by the determined. This article will unravel the complexities of secure file deletion and introduce a revolutionary method to safeguard your confidential information, ensuring it's truly gone.
The Illusion of Deletion: Why "Delete" Isn't Enough
Most of us rely on the "delete" key or the "move to recycle bin/trash" function to remove files. However, this is merely an instruction to the operating system, not a complete erasure. When you "delete" a file, the operating system typically marks the space on your hard drive or solid-state drive (SSD) as available for reuse. The data itself remains, invisibly, until overwritten by new information. Until then, the file’s remnants, comprising potentially confidential information, are susceptible to recovery through readily available data recovery software. This is akin to tearing up a paper document but leaving the individual pieces scattered. Anyone with enough time and the right tools can potentially reassemble it.
This lingering data presents a substantial risk. Consider sensitive company documents, client data, financial records, intellectual property, or personal information. If this data falls into the wrong hands, the consequences could be devastating, ranging from corporate espionage and identity theft to legal ramifications and reputational damage. Understand that the usual delete function is not a secure method. It is the first step, however.
Understanding the Mechanics of Data Storage and Recovery
To truly understand secure deletion, it's essential to grasp the underlying principles of data storage. Traditional hard disk drives (HDDs) store data magnetically on platters. When a file is "deleted," the operating system simply removes the pointers that indicate where the file is located. The actual data remains magnetically encoded on the platter until new data is written over it. Data recovery software can then scan the drive, identify these remnants, and reconstruct the files.
SSDs, on the other hand, employ a different technology. They use flash memory, which operates on the principle of electronically erasing and rewriting data blocks. While SSDs are generally faster than HDDs, they also present unique challenges regarding secure deletion. Due to the way SSDs manage wear leveling and other optimization techniques, "deleting" a file on an SSD may not always be as simple as overwriting the data sectors. The drive's internal controller might choose to move the data around, complicating the process of ensuring complete data destruction.
The Power of Overwriting: The Cornerstone of Secure Deletion
The primary objective of secure file deletion is to overwrite the data multiple times with random patterns, making it practically unrecoverable. This process renders the original data indecipherable, even with sophisticated recovery tools. This method is analogous to shredding a physical document multiple times, making it impossible to reconstruct the information. The more times the data is overwritten, the more secure the deletion becomes.
Several software solutions and tools are available that implement secure overwriting. These programs typically adhere to established data sanitization standards, such as those developed by the U.S. Department of Defense (DoD 5220.22-M), which specifies various overwriting processes. These standards dictate the number of passes and the specific patterns used to overwrite the data.
Introducing the Shocking Secret: Using an Online Secure File Eraser
The secret lies in a powerful, yet often overlooked, solution: dedicated online secure file erasers. These platforms offer a convenient and highly effective way to securely delete your work files, eliminating the complexities of installing and configuring software.
The advantages of using an online secure file eraser are numerous:
- Convenience: Access these tools from virtually any device with an internet connection, eliminating the need to install any software.
- Efficiency: These tools are designed to handle complex file deletion processes swiftly and efficiently, saving you valuable time.
- Security: They leverage advanced data sanitization algorithms, ensuring your files are overwritten multiple times, adhering to industry best practices.
- Peace of Mind: Gain the confidence that your data is permanently and securely destroyed, mitigating the risk of data breaches and unauthorized access.
The method is simple:
- Upload: Select the work files that you want to securely erase.
- Erase: Initiate the secure deletion process, choosing the appropriate algorithm and number of passes.
- Confirmation: Receive confirmation that the files have been securely overwritten and are no longer recoverable.
Choosing the Right Online Secure File Eraser: Key Considerations
When selecting an online secure file eraser, several factors are crucial to consider:
- Data Sanitization Algorithms: Ensure the tool utilizes robust, industry-recognized algorithms, such as those specified by the DoD 5220.22-M standard, to guarantee thorough data overwriting.
- Security and Privacy: Verify that the platform employs strong encryption and security protocols to protect your files during the upload and deletion process. Review the privacy policy to understand how your data is handled and stored.
- Compliance: If you operate within a regulated industry (e.g., finance, healthcare), make sure the eraser complies with relevant data privacy regulations, such as GDPR or HIPAA.
- User Experience: Choose a user-friendly platform with a clear and intuitive interface, making the process of secure file deletion straightforward and hassle-free.
- File Size Limitations: Be aware of any file size limitations imposed by the service. Some platforms may have restrictions on the size of files that can be uploaded and securely deleted.
- Customer Support: Look for a platform that provides responsive and helpful customer support.
Best Practices for Secure File Management in the Workplace
While online secure file erasers are a valuable tool, it's equally important to implement comprehensive best practices for secure file management in your workplace:
- Regular Data Sanitization: Implement a schedule for regularly sanitizing sensitive data, especially before disposing of old computers, hard drives, or other storage devices.
- Employee Training: Educate employees on the importance of secure file deletion and the proper use of the tools available. Teach the risks associated with inadequate deletion.
- Access Controls: Implement strong access controls to restrict access to sensitive files and limit the number of people who have access to them.
- Data Encryption: Encrypt sensitive files to add an extra layer of protection. While encryption protects the data, it also needs to be handled through secure processes.
- Secure Disposal of Physical Media: If you use removable media (USB drives, external hard drives, etc.), ensure that they are securely wiped or physically destroyed before disposal.
- Regularly Review and Update Policies: Review and update your data security policies regularly to address new threats and evolving regulations.
The Future of Secure Data Erasure
The ongoing advancement of technology will continue to shape the landscape of data erasure. As storage technologies evolve, new techniques and algorithms will emerge to counter potential vulnerabilities. Secure online file erasers are likely to become increasingly sophisticated, offering enhanced security features and integration with various cloud storage platforms. Expect to see a greater emphasis on automation, artificial intelligence, and blockchain technology to further enhance the security and transparency of the data erasure process.
Take Action Now: Safeguard Your Data
Don't leave your work files vulnerable to potential breaches. Protect your sensitive information by employing the shockingly effective method of using an online secure file eraser. Embrace the power of secure deletion and gain peace of mind, knowing that your data is permanently and irretrievably gone. Act now to protect your confidential information and mitigate the risks associated with data leakage. With just a few clicks, you can secure your data, protect your business, and preserve your reputation. Choose the right online secure file eraser today and experience the power of true data security.
